M4E Research #2: October 2023
Industry 4.0 and Beyond: The Role of 5G, WiFi 7, and TSN in Enabling Smart Manufacturing
Abstract: This paper explores the role that 5G, WiFi-7, and Time-Sensitive Networking (TSN) can play in driving smart manufacturing as a fundamental part of the Industry 4.0 vision. The paper provides an in-depth analysis of each technology's application in industrial communications, with a focus on TSN and its key elements that enable reliable and secure communication in industrial networks. In addition, the paper includes a comparative study of these technologies, analyzing them based on a number of industrial use-cases, supported secondary applications, industry adoption, and current market trends. The paper concludes by highlighting the challenges and future directions for the adoption of these technologies in industrial networks and emphasizes their importance in realizing the Industry 4.0 vision within the context of smart manufacturing.
Authors: Jobish John, Md. Noor-A-Rahim, Aswathi Vijayan, H. Vincent Poor, Dirk Pesch
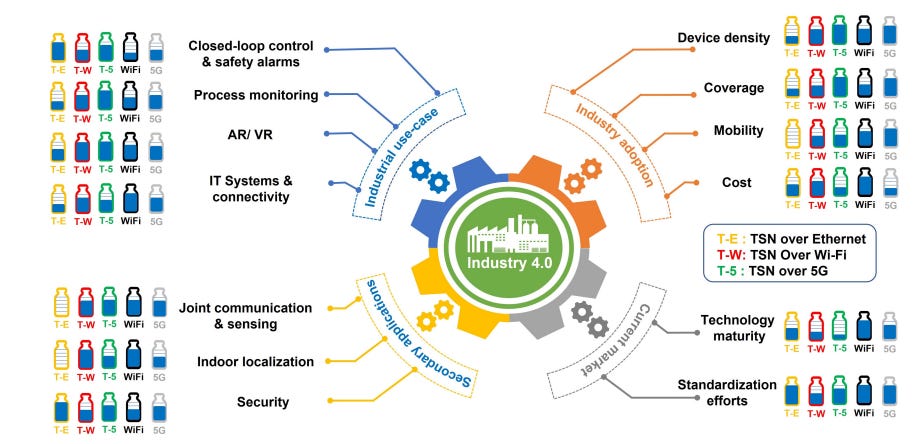
Discussion: Time-Sensitive Networking (TSN) refers to a set of standards within the IEEE 802.1 working group that aims to enhance the capabilities of Ethernet networks for time-critical applications. TSN is designed to provide deterministic and low-latency communication in industrial automation and other time-sensitive applications. WiFi-7 and 5G will also enable several use cases in manufacturing. You can check the image above (extracted from the paper) to see fast a comparison between these technologies applied to manufacturing use cases.
Link: https://arxiv.org/abs/2310.02379
Time-Series Classification in Smart Manufacturing Systems: An Experimental Evaluation of State-of-the-Art Machine Learning Algorithms
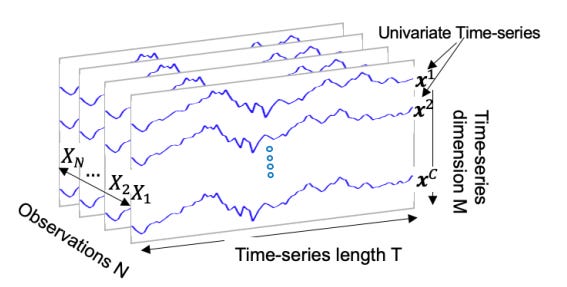
Abstract: Manufacturing is gathering extensive amounts of diverse data, thanks to the growing number of sensors and rapid advances in sensing technologies. Among the various data types available in SMS settings, time-series data plays a pivotal role. Hence, TSC emerges is crucial in this domain. The objective of this study is to fill this gap by providing a rigorous experimental evaluation of the SoTA ML and DL algorithms for TSC tasks in manufacturing and industrial settings. We first explored and compiled a comprehensive list of more than 92 SoTA algorithms from both TSC and manufacturing literature. Following, we selected the 36 most representative algorithms from this list. To evaluate their performance across various manufacturing classification tasks, we curated a set of 22 manufacturing datasets, representative of different characteristics that cover diverse manufacturing problems. Subsequently, we implemented and evaluated the algorithms on the manufacturing benchmark datasets, and analyzed the results for each dataset. Based on the results, ResNet, DrCIF, InceptionTime, and ARSENAL are the top-performing algorithms, boasting an average accuracy of over 96.6% across all 22 manufacturing TSC datasets. These findings underscore the robustness, efficiency, scalability, and effectiveness of convolutional kernels in capturing temporal features in time-series data, as three out of the top four performing algorithms leverage these kernels for feature extraction. Additionally, LSTM, BiLSTM, and TS-LSTM algorithms deserve recognition for their effectiveness in capturing features within time-series data using RNN-based structures.
Authors: Mojtaba A. Farahani, M. R. McCormick, Ramy Harik, Thorsten Wuest
Discussion: This paper presents a thorough analysis of time series classification algorithms with 36 of them analyzed, narrowing down the list from a total of 92 identified in the state of the art. The results of the study highlight the performance of several algorithms in handling time-series data across 22 datasets. Notably, ResNet, DrCIF, InceptionTime, and ARSENAL emerged as top-performing algorithms, showcasing an impressive average accuracy of over 96.6%. A key observation is that both DrCIF and ARSENAL, belonging to the conventional machine learning (ML) algorithms category, demonstrated competitiveness comparable to deep learning (DL) algorithms. This challenges the common notion that DL algorithms are always the optimal choice and underscores the existence of powerful alternatives.
Link: https://arxiv.org/abs/2310.02812
Graph-Theoretic Approach for Manufacturing Cybersecurity Risk Modeling and Assessment
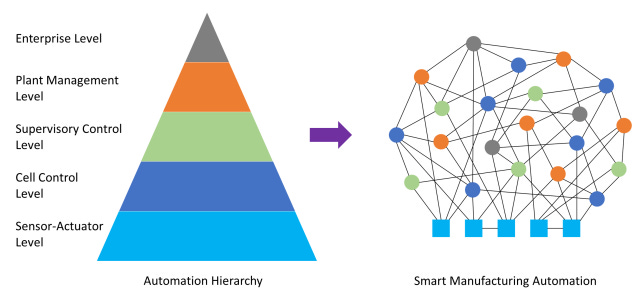
Abstract: Identifying, analyzing, and evaluating cybersecurity risks are essential to assess the vulnerabilities of modern manufacturing infrastructures and to devise effective decision-making strategies to secure critical manufacturing against potential cyberattacks. In response, this work proposes a graph-theoretic approach for risk modeling and assessment to address the lack of quantitative cybersecurity risk assessment frameworks for smart manufacturing systems. In doing so, first, threat attributes are represented using an attack graphical model derived from manufacturing cyberattack taxonomies. Attack taxonomies offer consistent structures to categorize threat attributes, and the graphical approach helps model their interdependence. Second, the graphs are analyzed to explore how threat events can propagate through the manufacturing value chain and identify the manufacturing assets that threat actors can access and compromise during a threat event. Third, the proposed method identifies the attack path that maximizes the likelihood of success and minimizes the attack detection probability, and then computes the associated cybersecurity risk. Finally, the proposed risk modeling and assessment framework is demonstrated via an interconnected smart manufacturing system illustrative example. Using the proposed approach, practitioners can identify critical connections and manufacturing assets requiring prioritized security controls and develop and deploy appropriate defense measures accordingly.
Authors: Md Habibor Rahman, Erfan Yazdandoost Hamedani, Young-Jun Son, Mohammed Shafae
Discussion: This paper addresses a critical aspect of modern manufacturing (cybersecurity risks) and proposes a graph-theoretic approach for modeling and assessing them within the context of smart manufacturing systems. The proposed framework is positioned as a critical step toward assisting both researchers and practitioners in identifying crucial connections and assets within discrete manufacturing systems. It not only aids in understanding how these assets can be exploited by different attack vectors but also informs decision-makers about prioritizing security investments.